AI as the driving force behind operational excellence
How security solutions are evolving from simple data capture to intelligent analysis, automated incident assessment and integrated platforms
The quiet paradigm shift in security analysis
Physical security infrastructure is undergoing a profound technological transformation – though less through spectacular individual innovations than through the continuous development of existing systems towards intelligent, context-based analysis. Whilst traditional video surveillance was primarily focused on storage and downstream evaluation, modern AI-based solutions enable the immediate interpretation of events in real time.
The focus is no longer simply on the detection of objects or movements, but on the ability to semantically interpret data, recognise connections and automatically provide relevant information. Security is thus increasingly becoming an information-driven process that directly supports operational decisions.
Development trends: From pixel-based detection to contextual analysis
The technological evolution of AI-supported security systems can be traced through several stages of development:
- Early phase: Movement as the central signal: Originally, systems were based on simple motion detection within defined image areas. The analysis was purely technical and lacked any interpretation of content.
- Expansion through external AI modules: With the integration of external computer vision solutions, the first semantic functions were added, such as the recognition of personal characteristics. However, these extensions often remained isolated and lacked flexibility.
- Vertical integration of AI expertise: A decisive step forward was taken with the development of proprietary AI models. This allowed analysis functions to be more closely integrated with the hardware and continuously optimised – for example, through number plate recognition or sophisticated object classification.
- Spatio-temporal linking of events: Modern systems go a step further and analyse movement patterns within their context. Trajectories, locations and interactions are linked, creating a holistic understanding of processes for the first time.
- Semantic interaction with data: The introduction of natural language as an interface fundamentally simplifies access to security data.
- Users formulate search queries intuitively (“person without a helmet”, “vehicle at night”), whilst the AI handles the semantic interpretation.
- The new quality of analysis:
- Search, understand, summarise
- A key advancement lies in the way data is processed. Modern systems combine multiple levels of analysis:
- Semantic search: Complex queries including logical links
- Reverse image search: Similarity-based image search across large datasets
- Event summaries: Automatic consolidation of video footage into structured reports
- Contextualised alerts: Events are not only detected but prioritised by relevance
These functions significantly reduce the manual analysis workload and, in particular, speed up forensic evaluations.
Investigations reimagined: The role of the “Unified Timeline”
A particularly practical approach is the cross-camera linking of events. So-called “Unified Timelines” allow the movements of people or objects to be reconstructed across multiple locations.
- Identification of individuals based on physical characteristics
- Tracking of movement routes
- Visualisation on site plans
This transforms a multitude of isolated video sequences into a coherent sequence of events.
Security analyses thus gain in speed and precision.
From reaction to anticipation: AI-supported event detection
In parallel with improved analysis, the capability for automated event detection is also evolving:
- Slip and fall detection for health and safety
- Detection of conflict situations such as physical altercations
- Monitoring of safety regulations, such as the wearing of protective clothing
- Acoustic analysis, e.g. in the case of unusually loud noises
These functions expand the role of security systems from mere observation to active support of operational processes.
Technological foundation: The importance of hybrid architectures
The performance of modern AI applications depends significantly on the underlying architecture.
The combination of edge and cloud computing is particularly relevant:
Edge level:
- Processing directly on the camera
- Minimal latency for real-time applications
- Increased data sovereignty
Cloud level:
- Use of powerful models for complex analyses
- Rapid development through centralised updates
- Scalable processing of large data volumes
This architecture makes it possible to ensure both performance and flexibility – a key prerequisite for the deployment of modern AI.
Integration as a driver of efficiency: security systems are converging
Another trend is the increasing integration of previously separate systems. Video surveillance, access control and visitor management are being consolidated into a single platform.
Concrete benefits:
- Linking access events with video context
- Automated granting and revocation of access rights for visitors
- Real-time monitoring of security-critical situations such as ‘tailgating’
For users, this means one thing above all: fewer system disconnections and significantly more efficient processes.
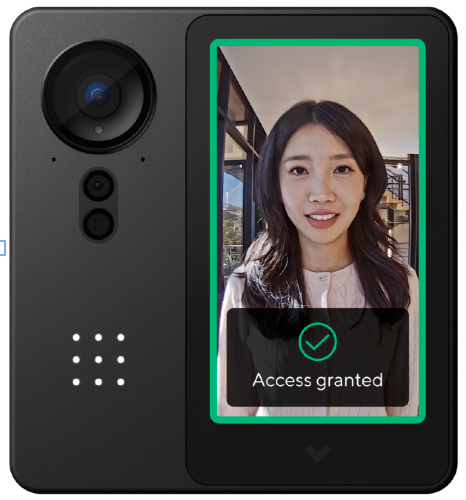
New access models: biometrics and contactless authentication
New possibilities are also emerging in the field of access control. Biometric methods such as facial recognition enable fast, contactless access whilst maintaining a high level of security.
Modern systems combine:
- Facial recognition using 3D and infrared technology
- Protective mechanisms against tampering (e.g. masks or images)
- Local processing of sensitive data
The focus is clearly on striking a balance between user convenience, security and data protection.
Data as operational added value
With increasing digitalisation, large volumes of security-relevant data are being generated. However, it is not the volume that is decisive, but its usability.
Modern platforms offer:
- Granular filtering and reporting functions
- Cross-site analyses
- Role-based access concepts
This makes security an integral part of corporate management – for instance, in the optimisation of processes or compliance with regulatory requirements.
Conclusion: Security is becoming intelligent, integrated and action-oriented
Current developments clearly show that the security industry is moving away from isolated technologies towards intelligently networked systems that not only collect data but also actively make it usable.
Three key trends are at the heart of this
- Semantic processing of data rather than mere storage
- Integration of various systems into a unified platform
- Automation of analysis and response through AI
For businesses, this means that security is increasingly becoming a strategic tool that goes far beyond traditional protection and actively contributes to efficiency, transparency and decision-making capability. [DCM]