Check Point says educational and research institutions are big targets for hackers during summer break.
Check Point Research (CPR), the threat intelligence division of Check Point® Software Technologies Ltd, a provider of cyber security solutions, has continued to monitor how hackers behave during the major summer holidays this summer.
Compared to other industries, the education and research sector is the most affected by cyber-attacks worldwide, with huge regional differences. This year, the sector recorded an average of 2256 weekly attacks per organisation globally, while the APAC region recorded the highest rate with an average of 4529 attacks per week, and North America the low with 1264. Europe ranked second with 2427 attacks per week per organisation – an 11 per cent increase over summer 2022 and by far the largest increase globally.
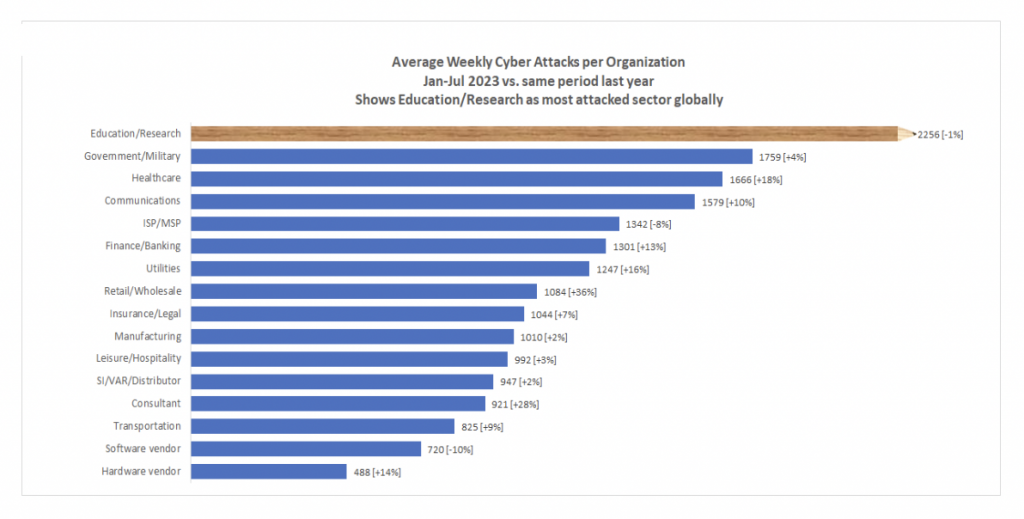
Figure 1: Average weekly cyber attacks per organisation by sector.
Second place by sector is taken by government and military with 1759 and third place by healthcare with 1666 average attacks per week per organisation globally.
Security researchers explain why this sector is so heavily attacked by the fact that, on the one hand, digitalisation has opened up numerous attack opportunities and, on the other hand, the sector has become very attractive with its large amount of sensitive pupil, student and research data, including private and financial information.
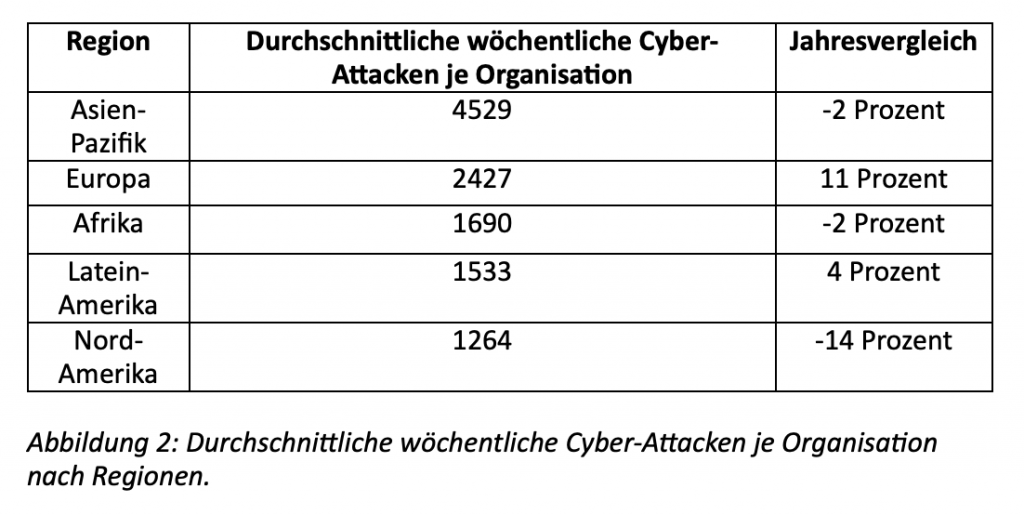
Figure 2: Average weekly cyber attacks per organisation by region.
How organisations should protect themselves:
- Robust data protection – A robust backup solution is an effective way to weaken the impact of a ransomware attack. If systems are backed up regularly, data loss from a ransomware attack should be minimal or non-existent.
- Up-to-date patches – Keeping computers up-to-date and applying patches, especially those deemed critical, is important to immediately reduce vulnerability to malware and ransomware attacks.
- Anti-ransomware solutions – Anti-ransomware solutions monitor programs for suspicious behaviours that are often associated with ransomware. When these behaviours are detected, the program can take immediate action to stop the encryption before further damage is done.
- Good threat prevention – Most malware and ransomware attacks can be detected and stopped before it is too late. Organisations need automated threat detection and defence to maximise their chances of protection through prevention.
- Employee training – If employees know what IT threats are lurking, how to recognise them and how to deal with them, this will strengthen the strongest line of defence, namely the human being, who will then not fall for a phishing email in the first place.
In addition, all those involved, whether parents, teachers, or pupils and students, should heed the following advice:
- Schools should always keep their IT systems up-to-date, install anti-virus programmes and activate automatic updates.
- Strong firewalls and gateways should be in place and third party vendors should be well vetted for their reputability.
- All staff should be trained to deal with the digital school world.
- Parents should educate their children about IT dangers, such as phishing, so that they do not click on links in emails before asking their parents.
- Decency rules should also apply in the digital world so that children do not send malicious messages or jokes, as well as recognise and report digital bullying immediately.
- Parents should drill into their children that they should never leave their networked devices lying around unattended because identity theft is in the hacker’s toolbox.
- Parental monitoring programmes help control traffic and internet surfing.
- Parents should invest time and money to educate their children for the digitalised world and its threats.
- Pupils and students should ensure that webcams are covered and microphones are automatically switched off when teaching online, so that they do not transmit until they are activated by them. In addition, private data of any kind should never be in the camera’s field of vision.
- Links and e-mails should be checked for their sender.
- Logging into the teaching portal should always be done directly, not via a link in an email.
- Strong passwords should be chosen for each user account.
- Sensitive information should never be shared via a cloud.
Read all the details here: https://blog.checkpoint.com/security/summer-break-isnt-a-vacation-for-cybercriminals-education-and-research-organizations-are-top-targets-according-to-check-point-research/





