- Automated scans open up a large field of potential victims for cybercriminals
- Ransomware, industrial espionage, misuse of pentest tools or sale of vulnerabilities by initial access brokers
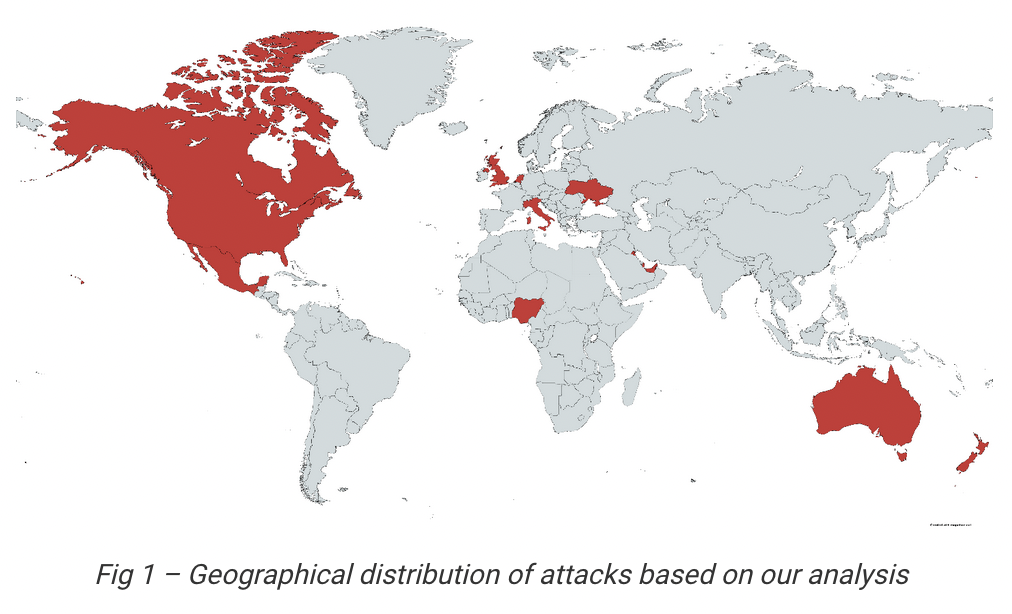
Using an opportunistic attack, cybercriminals have been targeting deployments of Zoho Corporation’s ManageEngine software solutions worldwide since January 2023. Bitdefender Labs has analysed the first attacks in its telemetry. The new campaign is another example of the more frequent opportunistic, initially automated search for vulnerabilities by cybercriminals, followed by hybrid targeted attacks. The goal of the attackers is to execute code remotely (Remote Code Execution – RCE) in order to play out further payload or to start industrial espionage. Potentially around 2,000 to 4,000 servers with internet access are currently affected worldwide. A patch is urgently recommended. ManageEngine had already published the report on the vulnerability CVE-2022-47966 on 10 January 2023, which affects 24 products.
ManageEngine, the enterprise IT management division of Zoho Corporation offers a comprehensive portfolio of real-time tools to monitor IT environments. Attacks on ManageEngine exploit CVE-2022-47966 have been on the rise worldwide since 20 January 2023, a remote code execution (RCE) that allows an unauthenticated attacker to completely take over compromised systems. A total of 24 different ManageEngine products are vulnerable. Two to four thousand servers with internet access have ManageEngine versions that are possible victims with the Proof of Concept (PoC) documented by the Horizon3.ai team. Not all servers can be attacked with this PoC because the XML framework Security Assertion Markup Language (SAML) must be configured.
Hybrid Spray-and-Pray Attacks in Trend
The current attacks are another example of an increasing trend to carry out scalable global attacks. The starting point is an automated opportunistic scan for an RCE vulnerability, often after a published PoC. Such attacks have already targeted Microsoft Exchange, Apache or VMware ESXI environments. The vulnerable systems discovered in the scan are then automatically compromised. As a result of such “spray-and-pray” tactics, even if many companies patch their systems, the cybercriminals can attack numerous other servers with internet connectivity.
Unleashed risk potential
For unpatched systems, the attackers then implement additional tools. Initial access brokers selling their knowledge of vulnerabilities attempted to initialise AnyDesk software for persistent remote access. In other cases, the perpetrators played out the payload of a new ransomware attack Buhti. Others attempted to play out the Cobalt Strike economic espionage simulation tool or the RAT-el-Red teaming tool for pentesting and alienate it for their purposes.
The attackers often modify the PoC only minimally. As a result, the immediate effect of an attack is only slight at first. Many victims therefore only react with temporary repairs or workarounds. The systems are then initially considered immune, but are open to the next modification by the attackers.
Companies should urgently patch their systems. Solutions that assess the reputation of IP addresses, doumans or URLs are also important. Extended detection and response approaches also help. External help from managed detection-and-response services also improves the defence against such attackers.
The complete study can be found here: https://businessinsights.bitdefender.com/tech-advisory-manageengine-cve-2022-47966