With the VISIT brand, ASTRUM IT GmbH, founded in 1992, has been impressing its customers for years. The VISIT visitor management software is a scalable solution that gives you a 360° view of the factory site.
The system offers a synthesis of digital visitor management, logistics management and a training tool! From appointment coordination to registration and employee training, all processes can be combined with just one software. By integrating multi-level approval workflows directly into the visitor management process, sensitive areas and critical work processes in the company are now protected easily and efficiently.
VISIT – NEW MODULE VISIT Secure – Approval Workflow
The Erlangen software experts for digital vitality have extended their VISIT brand with the new module VISIT Secure – Approval Workflow. The registration process is simplified by automated workflows for employees, processed in a comprehensible manner and seamlessly documented at all times.
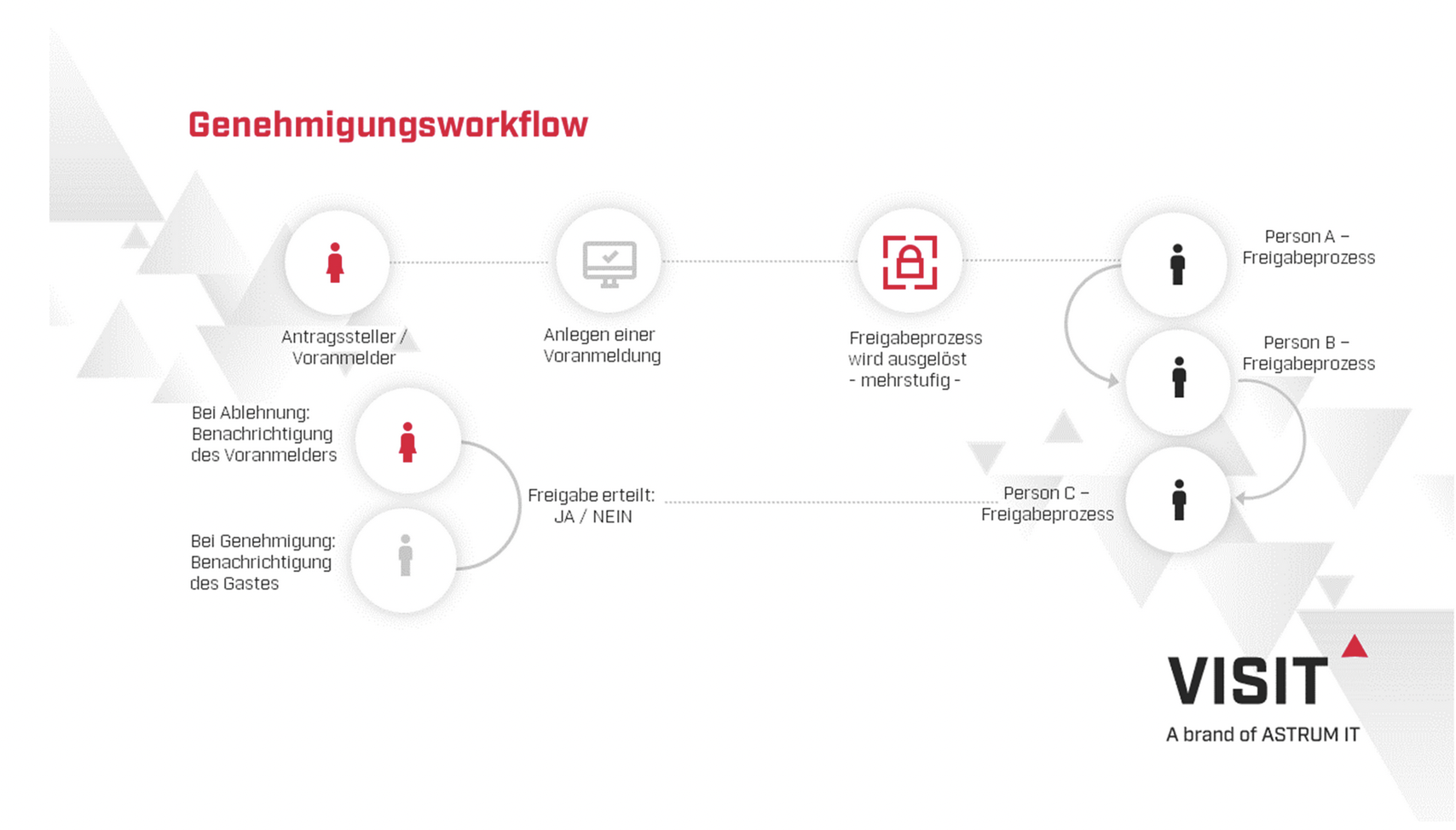
With VISIT Secure – Approval Workflow, the approval process is automatically integrated into the visitor registration. As soon as certain areas within the plant premises require special protection, measures must be taken to shield them from unwanted access.
As soon as an employee creates a pre-registration for a visitor and triggers a process that requires approval, predefined groups of people or the visited employees in the company receive a notification by e-mail. Only after approval by the employee(s) can the visit begin.
Approval workflows: efficient and simple
It is also efficient and simple. Time and effort are kept in check and the focus remains on the important things. Nevertheless, security measures are significantly increased. Why? The approval process builds additional (multi-level) security layers into the visit process, creating a higher level of protection for the plant site, sensitive areas and employees. At the same time, all necessary legal requirements such as DSGVO-compliant storage of personal data are taken into account within the process flow.